ALWAYS-ON DEFENSE AGAINST CYBER THREATS
Stop attacks in seconds with real-time mitigation and local 24/7 oversight.
Ready to Strengthen Your Defenses?
"*" indicates required fields


A Distributed Denial of Service (DDoS) attack can hit in seconds. Botnets can flood your systems with junk traffic until real users can’t get through. Transactions fail. Applications stall. Every minute costs you revenue, time, and trust.
DQE’s DDoS Mitigation shuts down the threat before it reaches your operations. With always-on monitoring, intelligent filtering, and real-time response, we stop volumetric floods, application-layer strikes, and multi-vector campaigns in their tracks while legitimate traffic keeps flowing. Backed by our utility-grade network and Pittsburgh-based engineers, your defenses stay as sharp and responsive as the attackers are relentless.

What Makes DQE Reliably Different
Not all protection is created equal. DQE delivers enterprise-grade resilience designed for critical infrastructure.
Who We Serve

Financial Services
Keep customer transactions and financial platforms running even under attack.

Healthcare
Ensure patient services and clinical applications stay connected without disruption.

Manufacturing and Logistics
Protect production lines, supply chains, and IoT systems from costly downtime.

Government and Public Services
Maintain secure, continuous access to critical citizen-facing platforms.

E-Commerce and Digital Platforms
Prevent outages during peak traffic, preserving sales and customer trust.
Ready for Fiber You Can Count On?
Let’s figure out what’s right for you without the hassle.
"*" indicates required fields
View Our NETWORK
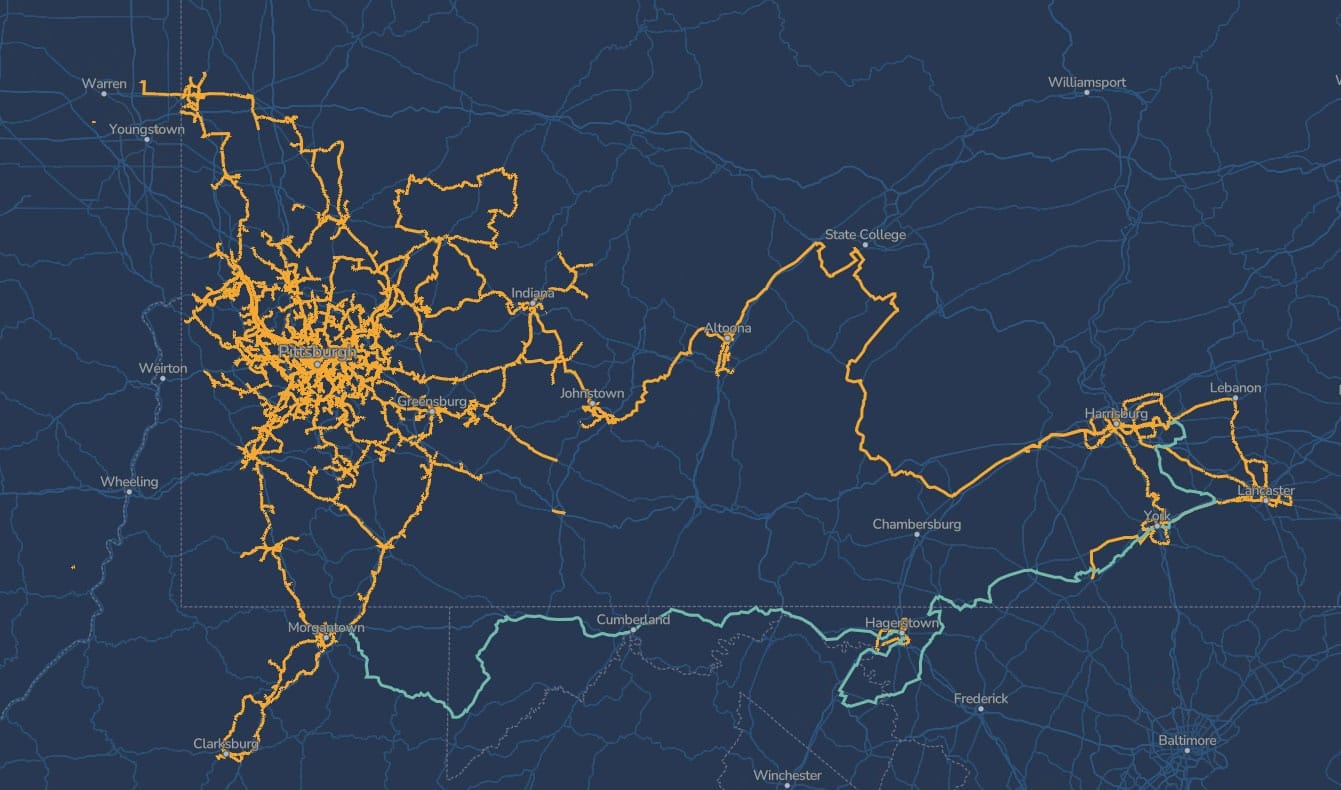
Serving Areas Across Pennsylvania, West Virginia, and Maryland
Our fiber network was built to utility standards and designed to grow with the region. From downtown Pittsburgh to surrounding communities, we connect businesses with reliable infrastructure that doesn’t quit. Enter your address to see if your site is already covered — and if it’s not, let’s talk about building to you.
SEARCH THE NETWORKAdditional Resources
Protected: Enterprise Network Reliability for AI W…
There is no excerpt because this is a protected post….
The Invisible Backbone of AI
Hyperscale Fiber Infrastructure in Pennsylvania: Why Regional Networks Win Hyperscale AI sites are chosen for power firs…
The Local Advantage: How Community-Based Fiber Pro…
By Nikki Marsh, Chief Revenue Officer, DQE Communications The local fiber narrative is quietly transforming how busine…