UNIFIED PROTECTION WITHOUT THE OVERHEAD
Reliably reliable cyber-security. Delivered by the same people who built your network.
Ready to Simplify Security?
"*" indicates required fields


Building a full-scale security operation in-house takes deep pockets and a 24/7 team. DQE gives you another option.
With DDoS protection, managed firewalls, and SOCaaS (Security Operations Center as a Service) working together, you get layered defense without the overhead. Everything is deployed, monitored, and maintained by local engineers who move fast, communicate clearly, and own your uptime.
Because reliability isn’t just about staying online, it’s knowing the people behind your network respond before the second ring.

THREE LAYERS OF DEFENSE
Protection that adapts to your business — and grows with it.
Comprehensive protection designed to evolve with your business needs while ensuring compliance, continuity, and confidence

POWERED BY FORTINET
Enterprise Performance. Fortinet Power. DQE Expertise.
DQE’s Managed Security solutions are built on Fortinet, recognized as a 2024 Gartner® Magic Quadrant™ Leader for SD-WAN and Security Service Edge. Fortinet’s Unified Threat Protection delivers enterprise-grade security with advanced malware protection, intrusion prevention, and comprehensive web filtering — all working together to protect your organization from evolving threats.
With Fortinet’s award-winning technology and DQE’s local security expertise, you get industry-leading protection managed by engineers who understand the threat landscape businesses face in your region.
Who We PROTECT




Ready for Fiber You Can Count On?
Let’s figure out what’s right for you without the hassle.
"*" indicates required fields
View Our NETWORK
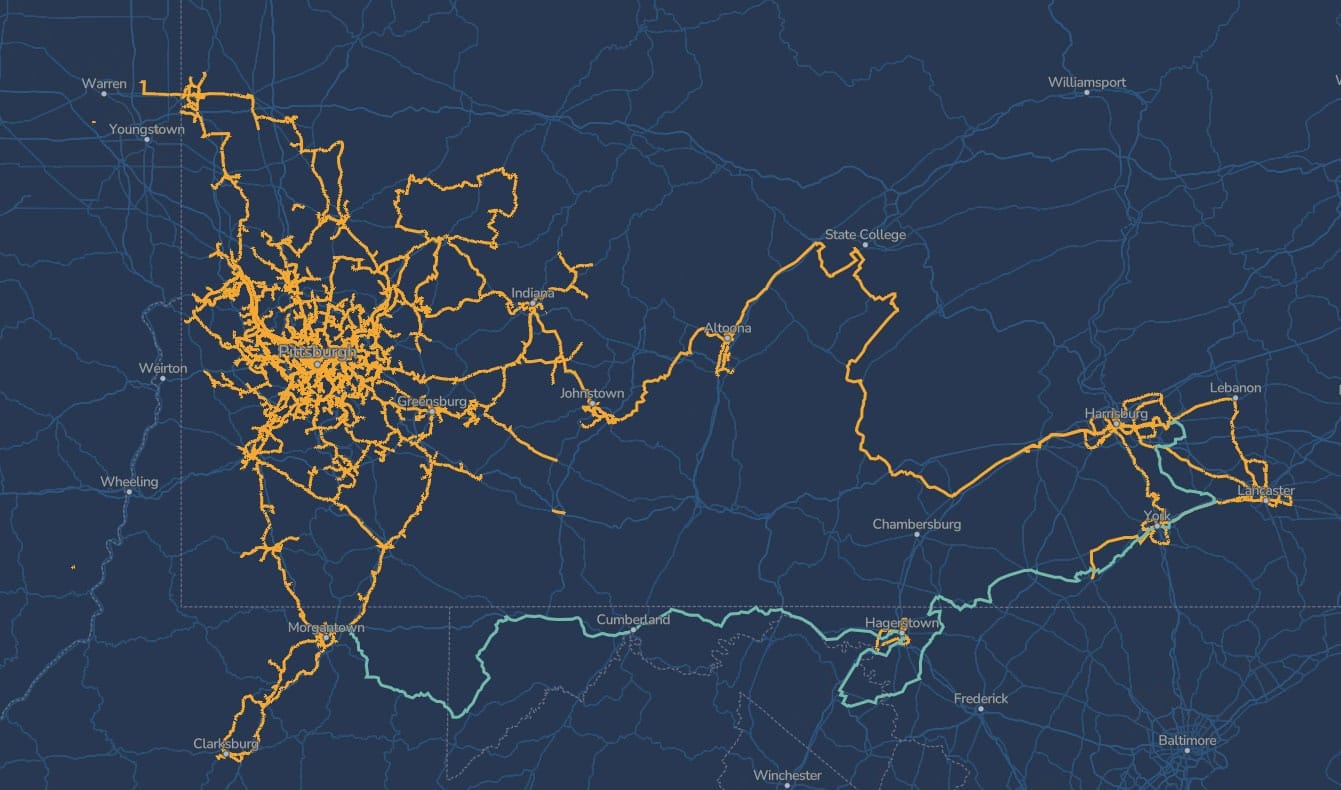
Serving Areas Across Pennsylvania, West Virginia, and Maryland
Our fiber network was built to utility standards and designed to grow with the region. From downtown Pittsburgh to surrounding communities, we connect businesses with reliable infrastructure that doesn’t quit. Enter your address to see if your site is already covered — and if it’s not, let’s talk about building to you.
SEARCH THE NETWORKAdditional Resources
DQE Communications CEO Mike Sicoli Featured in Inv…
PITTSBURGH, PA — DQE Communications CEO Mike Sicoli was featured in Invest: Pittsburgh 3rd Edition, a regional busines…
DQE Communications Announces Brand Refresh and Exp…
PITTSBURGH, January 29, 2025 – DQE Communications, a leading, regional business connectivity solutions provider, today…
Penn State and Carnegie Mellon researchers track g…
In many cities, aging infrastructure, climate change, and urban geohazards – such as flooding, sewer leaks, and landsl…